Generate A Hash Key C++
- Perl Hash Key
- Generate Hash Online
- Hash Key On Keyboard
- Generate A Hash Key C Key
- Generate A Hash Key C Code
- Generate A Hash Key C Youtube
Perl Hash Key
- MD5 hashes are also used to ensure the data integrity of files. Because the MD5 hash algorithm always produces the same output for the same given input, users can compare a hash of the source file with a newly created hash of the destination file to check that it is intact and unmodified. An MD5 hash is NOT encryption.
- Sep 14, 2015 Below is the Hash Map implementation in C. HashMap class contains the hash table, which is a double pointer to HashNode class and default table size in constant is used to construct this hash.
- MD5 Hash Generator This online tool allows you to generate the MD5 hash of any string. The MD5 hash can not be decrypted if the text you entered is complicated enough.
- Dec 10, 2018 How to create an unorderedmap of pairs in C? Unordered Map does not contain a hash function for a pair like it has for int, string, etc, So if we want to hash a pair then we have to explicitly provide it with a hash function that can hash a pair. Unorderedmap can takes upto 5 arguments.
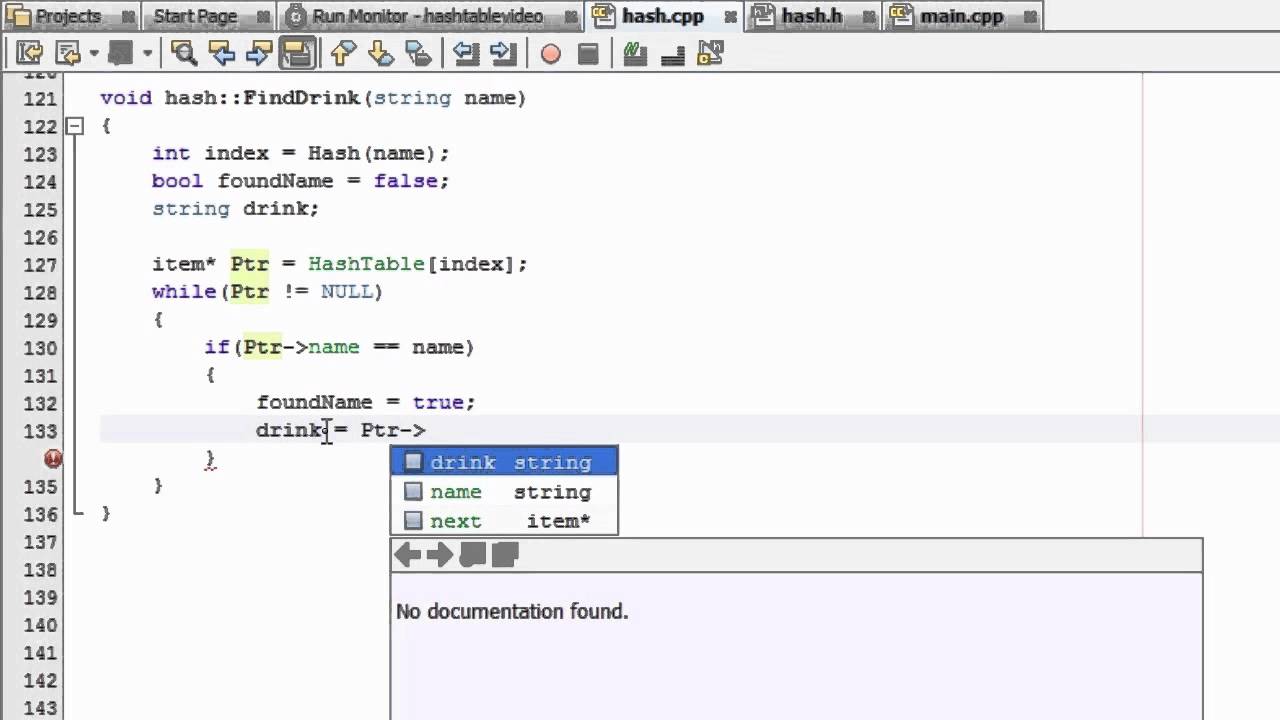
- Jul 17, 2013 In this tutorial, I show how to create a function that will determine if a key is in the hash table. If a key is in the table, the function grabs and displays the associated value. Want to learn C?
MD5 hashes are also used to ensure the data integrity of files. Because the MD5 hash algorithm always produces the same output for the same given input, users can compare a hash of the source file with a newly created hash of the destination file to check that it is intact and unmodified.
Definition
Computes a Hash-based Message Authentication Code (HMAC) using the SHA512 hash function.
- Attributes
Examples
The following example shows how to sign a file by using the HMACSHA512 object and then how to verify the file. Pc speed maximizer key generator.
Remarks
HMACSHA512 is a type of keyed hash algorithm that is constructed from the SHA-512 hash function and used as a Hash-based Message Authentication Code (HMAC). The HMAC process mixes a secret key with the message data and hashes the result. The hash value is mixed with the secret key again, and then hashed a second time. The output hash is 512 bits in length.
An HMAC can be used to determine whether a message sent over a nonsecure channel has been tampered with, provided that the sender and receiver share a secret key. The sender computes the hash value for the original data and sends both the original data and hash value as a single message. The receiver recalculates the hash value on the received message and checks that the computed HMAC matches the transmitted HMAC.
If the original and computed hash values match, the message is authenticated. If they do not match, either the data or the hash value has been changed. HMACs provide security against tampering because knowledge of the secret key is required to change the message and reproduce the correct hash value.
HMACSHA512 accepts keys of any size, and produces a hash sequence of length 512 bits.
Constructors
Generate Hash Online
| HMACSHA512() | Initializes a new instance of the HMACSHA512 class with a randomly generated key. |
| HMACSHA512(Byte[]) | Initializes a new instance of the HMACSHA512 class with the specified key data. |
Fields
| HashSizeValue | Represents the size, in bits, of the computed hash code. (Inherited from HashAlgorithm) |
| HashValue | Represents the value of the computed hash code. (Inherited from HashAlgorithm) |
| KeyValue | The key to use in the hash algorithm. (Inherited from KeyedHashAlgorithm) |
| State | Represents the state of the hash computation. (Inherited from HashAlgorithm) |
Properties
| BlockSizeValue | Gets or sets the block size to use in the hash value. (Inherited from HMAC) |
| CanReuseTransform | Gets a value indicating whether the current transform can be reused. (Inherited from HashAlgorithm) |
| CanTransformMultipleBlocks | When overridden in a derived class, gets a value indicating whether multiple blocks can be transformed. (Inherited from HashAlgorithm) |
| Hash | Gets the value of the computed hash code. (Inherited from HashAlgorithm) |
| HashName | Gets or sets the name of the hash algorithm to use for hashing. (Inherited from HMAC) |
| HashSize | Gets the size, in bits, of the computed HMAC. |
| InputBlockSize | When overridden in a derived class, gets the input block size. (Inherited from HashAlgorithm) |
| Key | Gets or sets the key to use in the HMAC calculation. |
| OutputBlockSize | When overridden in a derived class, gets the output block size. (Inherited from HashAlgorithm) |
| ProduceLegacyHmacValues | Provides a workaround for the .NET Framework 2.0 implementation of the HMACSHA512 algorithm, which is inconsistent with the .NET Framework 2.0 Service Pack 1 implementation. |
Hash Key On Keyboard
Methods
| Clear() | Releases all resources used by the HashAlgorithm class. (Inherited from HashAlgorithm) |
| ComputeHash(Byte[]) | Computes the hash value for the specified byte array. (Inherited from HashAlgorithm) |
| ComputeHash(Byte[], Int32, Int32) | Computes the hash value for the specified region of the specified byte array. (Inherited from HashAlgorithm) |
| ComputeHash(Stream) | Computes the hash value for the specified Stream object. (Inherited from HashAlgorithm) |
| ComputeHashAsync(Stream, CancellationToken) | (Inherited from HashAlgorithm) |
| Dispose() | Releases all resources used by the current instance of the HashAlgorithm class. (Inherited from HashAlgorithm) |
| Dispose(Boolean) | Releases the unmanaged resources used by the HMACSHA512 and optionally releases the managed resources. |
| Equals(Object) | Determines whether the specified object is equal to the current object. (Inherited from Object) |
| GetHashCode() | Serves as the default hash function. (Inherited from Object) |
| GetType() | Gets the Type of the current instance. Simcity 5 beta key generator. You can download the tool with just a few and easy configuration steps. (Inherited from Object) |
| HashCore(Byte[], Int32, Int32) | Routes data written to the object into the HMAC algorithm for computing the HMAC. |
| HashCore(ReadOnlySpan<Byte>) | Routes data written to the object into the HMAC algorithm for computing the HMAC. |
| HashFinal() | Finalizes the HMAC computation after the last data is processed by the algorithm. |
| Initialize() | Resets the hash algorithm to its initial state. |
| MemberwiseClone() | Creates a shallow copy of the current Object. (Inherited from Object) |
| ToString() | Returns a string that represents the current object. (Inherited from Object) |
| TransformBlock(Byte[], Int32, Int32, Byte[], Int32) | Computes the hash value for the specified region of the input byte array and copies the specified region of the input byte array to the specified region of the output byte array. (Inherited from HashAlgorithm) |
| TransformFinalBlock(Byte[], Int32, Int32) | Computes the hash value for the specified region of the specified byte array. (Inherited from HashAlgorithm) |
| TryComputeHash(ReadOnlySpan<Byte>, Span<Byte>, Int32) | Attempts to compute the hash value for the specified byte array. (Inherited from HashAlgorithm) |
| TryHashFinal(Span<Byte>, Int32) | Attempts to finalize the HMAC computation after the last data is processed by the HMAC algorithm. |
Explicit Interface Implementations
Generate A Hash Key C Key
| IDisposable.Dispose() | Releases the unmanaged resources used by the HashAlgorithm and optionally releases the managed resources. (Inherited from HashAlgorithm) |