Visual Studio Generate Strong Name Key File
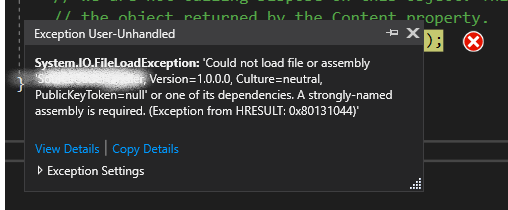
Jan 22, 2015 Cannot import the following key file: magellanicKey.pfx. The key file may be password protected. To correct this, try to import the certificate again or manually install the certificate to the Strong Name CSP with the following key container name: VSKEY883A9453A40E283F. To configure a strong name assembly key file Start Visual Studio Command Prompt. At the command prompt, from the folder where you want to store the key file. In Visual Studio Solution Explorer, right-click the project and then click Properties. Click the Signing tab and choose Browse in the.
- Visual Studio Generate Strong Name Key File For Windows 10
- Visual Studio Generate Strong Name Key File For Mac
To sign an assembly with a strong name, you must have a public/private key pair. This public and private cryptographic key pair is used during compilation to create a strong-named assembly. You can create a key pair using the Strong Name tool (Sn.exe). Key pair files usually have an .snk extension.
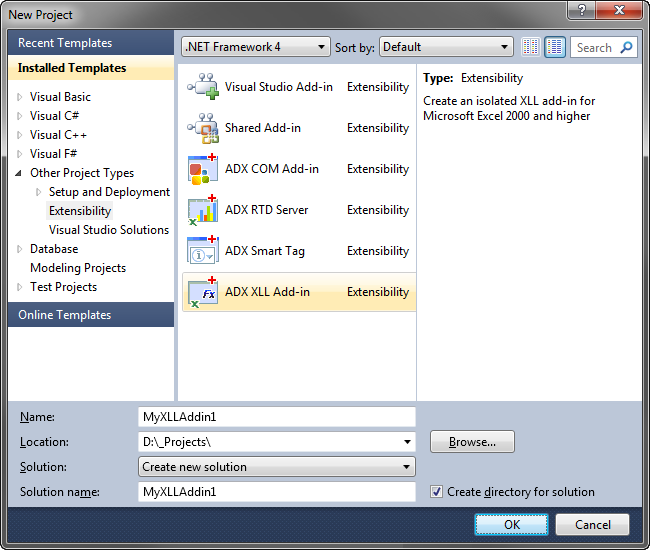
Since then I found out that I can use sn.exe to add and delete keys to/from the Strong Name CSP. One problem that I'm still having is that Visual Studio seems to generate a random container name for the key, so I don't know how to delete the one associated with my project. You can't use sn.exe to list all container names either. Global Assembly Cache To create a small Class Library project by using Visual Studio, to generate a strong name, and to install the.dll file of the project in the GAC, follow these steps: In Visual Studio, create a new Visual C# Class Library project, and name the project GACDemo. You must use a strong name. In Visual Studio, the C# and Visual Basic project property pages include a Signing tab that enables you to select existing key files or to generate new key files without using Sn.exe. Visual Studio. Visual Studio for Mac.NET. Azure DevOps. Azure DevOps Server (TFS) 0. Creating Strong Name Key - The operation could not be completed. Invalid provider type specified. Windows 10.0 visual studio 2017 version 15.5. Curtis A DeHart II reported Jan 06, 2018 at 03:37 AM. Apr 25, 2013 Hello. Having issue building an application with signing turned on for strong name key file. We've been building clickone applications w/o problems for a long time. Dont' have issues with this. We normally would take the keyfile, log into our build servers as the account that is doing the. Hi kpdn, Thanks for your post! Do you mean you cannot.
Note
In Visual Studio, the C# and Visual Basic project property pages include a Signing tab that enables you to select existing key files or to generate new key files without using Sn.exe. In Visual C++, you can specify the location of an existing key file in the Advanced property page in the Linker section of the Configuration Properties section of the Property Pages window. The use of the AssemblyKeyFileAttribute attribute to identify key file pairs was made obsolete beginning with Visual Studio 2005.
Create a key pair
To create a key pair, at a command prompt, type the following command:
sn –k <file name>
In this command, file name is the name of the output file containing the key pair.
The initial and final permutations are shown as follows − Round FunctionThe heart of this cipher is the DES function, f. − After the expansion permutation, DES does XOR operation on the expanded right section and the round key. They have no cryptography significance in DES. Permutation logic is graphically depicted in the following illustration −.The graphically depicted permutation logic is generally described as table in DES specification illustrated as shown −.XOR (Whitener). Generating round keys in aes 2017. The DES function applies a 48-bit key to the rightmost 32 bits to produce a 32-bit output.Expansion Permutation Box − Since right input is 32-bit and round key is a 48-bit, we first need to expand right input to 48 bits.
The following example creates a key pair called sgKey.snk.
If you intend to delay sign an assembly and you control the whole key pair (which is unlikely outside test scenarios), you can use the following commands to generate a key pair and then extract the public key from it into a separate file. First, create the key pair:
Next, extract the public key from the key pair and copy it to a separate file:
Once you create the key pair, you must put the file where the strong name signing tools can find it.
Visual Studio Generate Strong Name Key File For Windows 10
When signing an assembly with a strong name, the Assembly Linker (Al.exe) looks for the key file relative to the current directory and to the output directory. When using command-line compilers, you can simply copy the key to the current directory containing your code modules.
If you are using an earlier version of Visual Studio that does not have a Signing tab in the project properties, the recommended key file location is the project directory with the file attribute specified as follows:
See also
-->A strong name consists of the assembly's identity—its simple text name, version number, and culture information (if provided)—plus a public key and a digital signature. It is generated from an assembly file using the corresponding private key. (The assembly file contains the assembly manifest, which contains the names and hashes of all the files that make up the assembly.)
Warning
Do not rely on strong names for security. They provide a unique identity only.
A strong-named assembly can only use types from other strong-named assemblies. Otherwise, the integrity of the strong-named assembly would be compromised.
Note
Although .NET Core supports strong-named assemblies, and all assemblies in the .NET Core library are signed, the majority of third-party assemblies do not need strong names. For more information, see Strong Name Signing on GitHub.
Strong name scenario
The following scenario outlines the process of signing an assembly with a strong name and later referencing it by that name.
Assembly A is created with a strong name using one of the following methods:
Using a development environment that supports creating strong names, such as Visual Studio.
Creating a cryptographic key pair using the Strong Name tool (Sn.exe) and assigning that key pair to the assembly using either a command-line compiler or the Assembly Linker (Al.exe). The Windows SDK provides both Sn.exe and Al.exe.
The development environment or tool signs the hash of the file containing the assembly's manifest with the developer's private key. This digital signature is stored in the portable executable (PE) file that contains Assembly A's manifest.
Assembly B is a consumer of Assembly A. The reference section of Assembly B's manifest includes a token that represents Assembly A's public key. A token is a portion of the full public key and is used rather than the key itself to save space.
The common language runtime verifies the strong name signature when the assembly is placed in the global assembly cache. When binding by strong name at run time, the common language runtime compares the key stored in Assembly B's manifest with the key used to generate the strong name for Assembly A. If the .NET Framework security checks pass and the bind succeeds, Assembly B has a guarantee that Assembly A's bits have not been tampered with and that these bits actually come from the developers of Assembly A.
Note
Visual Studio Generate Strong Name Key File For Mac
This scenario doesn't address trust issues. Assemblies can carry full Microsoft Authenticode signatures in addition to a strong name. Authenticode signatures include a certificate that establishes trust. It's important to note that strong names don't require code to be signed in this way. Strong names only provide a unique identity.
Bypass signature verification of trusted assemblies
Starting with the .NET Framework 3.5 Service Pack 1, strong-name signatures are not validated when an assembly is loaded into a full-trust application domain, such as the default application domain for the MyComputer zone. This is referred to as the strong-name bypass feature. In a full-trust environment, demands for StrongNameIdentityPermission always succeed for signed, full-trust assemblies, regardless of their signature. The strong-name bypass feature avoids the unnecessary overhead of strong-name signature verification of full-trust assemblies in this situation, allowing the assemblies to load faster.
The bypass feature applies to any assembly that is signed with a strong name and that has the following characteristics:
Fully trusted without StrongName evidence (for example, has
MyComputerzone evidence).Loaded into a fully trusted AppDomain.
Loaded from a location under the ApplicationBase property of that AppDomain.
Not delay-signed.
This feature can be disabled for individual applications or for a computer. See How to: Disable the strong-name bypass feature.
Related topics
| Title | Description |
|---|---|
| How to: Create a public-private key pair | Describes how to create a cryptographic key pair for signing an assembly. |
| How to: Sign an assembly with a strong name | Describes how to create a strong-named assembly. |
| Enhanced strong naming | Describes enhancements to strong-names in the .NET Framework 4.5. |
| How to: Reference a strong-named assembly | Describes how to reference types or resources in a strong-named assembly at compile time or run time. |
| How to: Disable the strong-name bypass feature | Describes how to disable the feature that bypasses the validation of strong-name signatures. This feature can be disabled for all or for specific applications. |
| Create assemblies | Provides an overview of single-file and multifile assemblies. |
| How to delay sign an assembly in Visual Studio | Explains how to sign an assembly with a strong name after the assembly has been created. |
| Sn.exe (Strong Name tool) | Describes the tool included in the .NET Framework that helps create assemblies with strong names. This tool provides options for key management, signature generation, and signature verification. |
| Al.exe (Assembly linker) | Describes the tool included in the .NET Framework that generates a file that has an assembly manifest from modules or resource files. |